Documentation Index
Fetch the complete documentation index at: https://ona.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Available on the Enterprise plan. Currently in beta. Contact sales to learn more.
How it works
When SCIM is configured, your identity provider communicates with Ona through a SCIM endpoint using a bearer token for authentication. Changes in your IdP directory — such as adding a new employee or disabling an account — are automatically reflected in your Ona organization. SCIM provisioning is linked to an existing SSO login provider. The linked SSO configuration determines how provisioned users authenticate when signing in to Ona.Prerequisites
- An active SSO login provider configured in your organization
- Admin-level access to your organization settings in Ona
- Admin access to your identity provider (e.g., Microsoft Entra ID)
Setting up SCIM in Ona
Step 1. Open SCIM configuration
Navigate to Organization Settings > Login and Security. Scroll to the SCIM Provisioning section.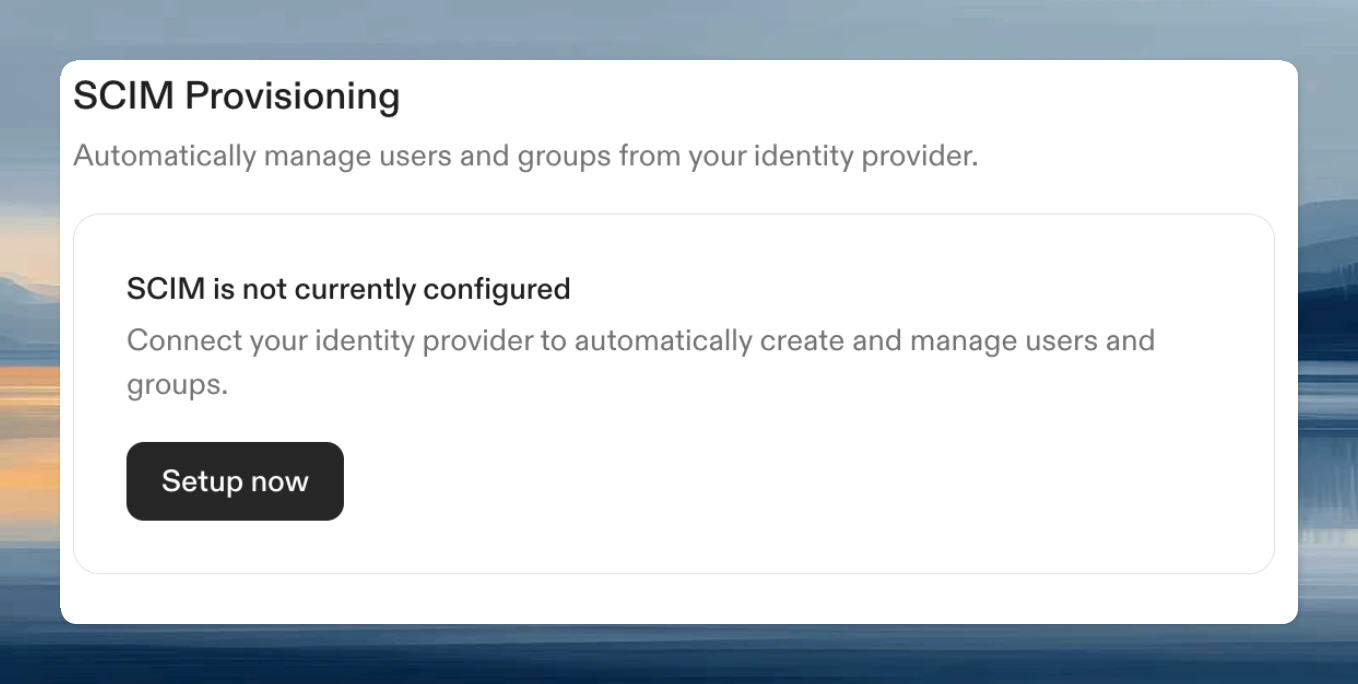
Step 2. Create a SCIM configuration
In the configuration dialog:- Select the Linked SSO configuration — this is the SSO provider that provisioned users will use to sign in
- Enter a Name for this SCIM configuration
- Click Create
Configuring your identity provider
Microsoft Entra ID
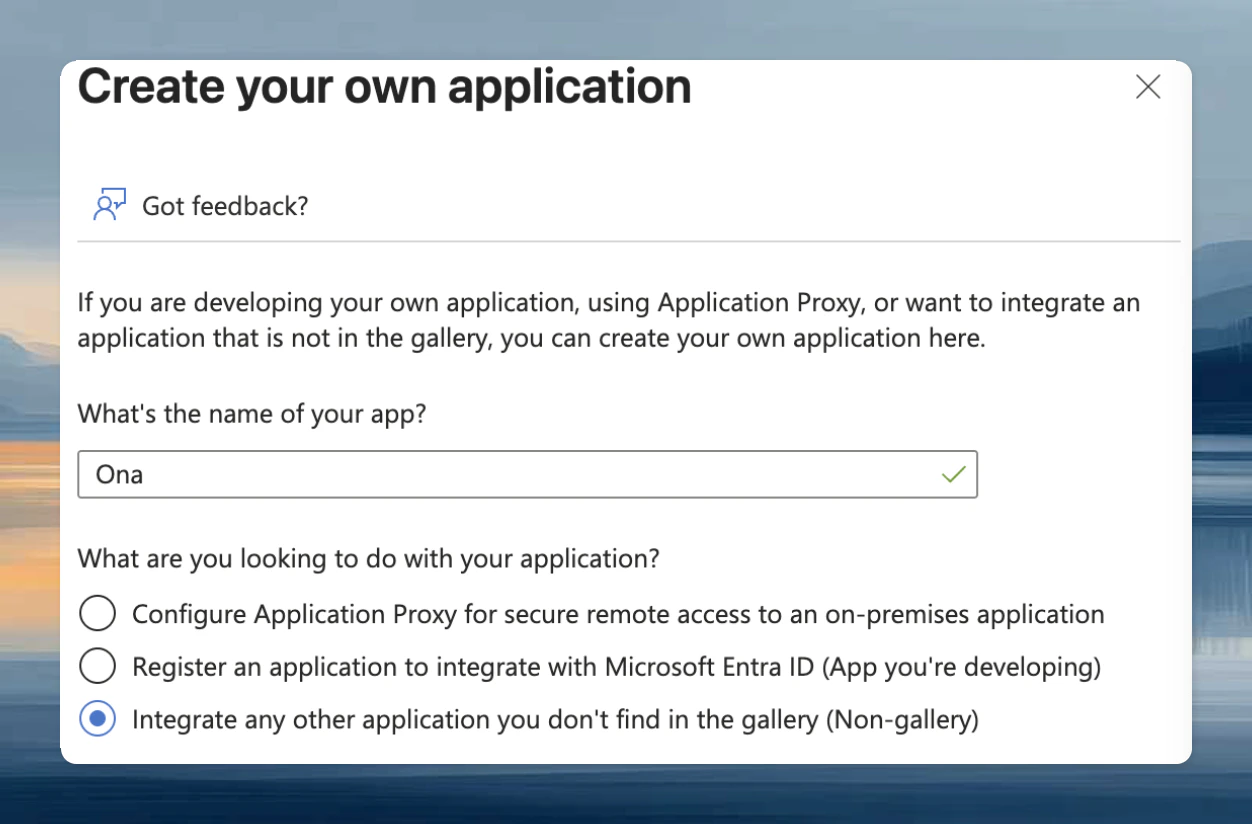
Creating an Enterprise Application
If you don’t already have an Enterprise Application for Ona, create one:- Open the Microsoft Entra admin center
- Navigate to Enterprise Applications
- Click New application, then select Create your own application
- Enter a name for the application (e.g.,
Ona) - Select Integrate any other application you don’t find in the gallery (Non-gallery)
- Click Create
Configuring provisioning
- In the Microsoft Entra admin center, navigate to Enterprise Applications and select the application you created for Ona
- Go to Provisioning and select Provisioning again
- Set Provisioning Mode to Automatic
- Under Admin Credentials, configure the following:
- Authentication Method: Bearer Authentication
- Tenant URL: Paste the SCIM endpoint URL from Ona
- Secret Token: Paste the bearer token from Ona
- Click Test Connection to verify the configuration
Scoping users
We recommend provisioning only the users who will use Ona, rather than your entire directory. You can control this with scoping filters in your identity provider. In Microsoft Entra:- In the Provisioning tab, select Mappings
- Open the mapping for Users or Groups
- Under Source Object Scope, add a Scoping Filter Group to limit which users are provisioned