Most policies require an Enterprise plan. Environment timeout is available on Core and Enterprise.
- Changes take effect immediately for new actions
- Existing environments are not affected unless the policy governs a scheduled lifecycle action
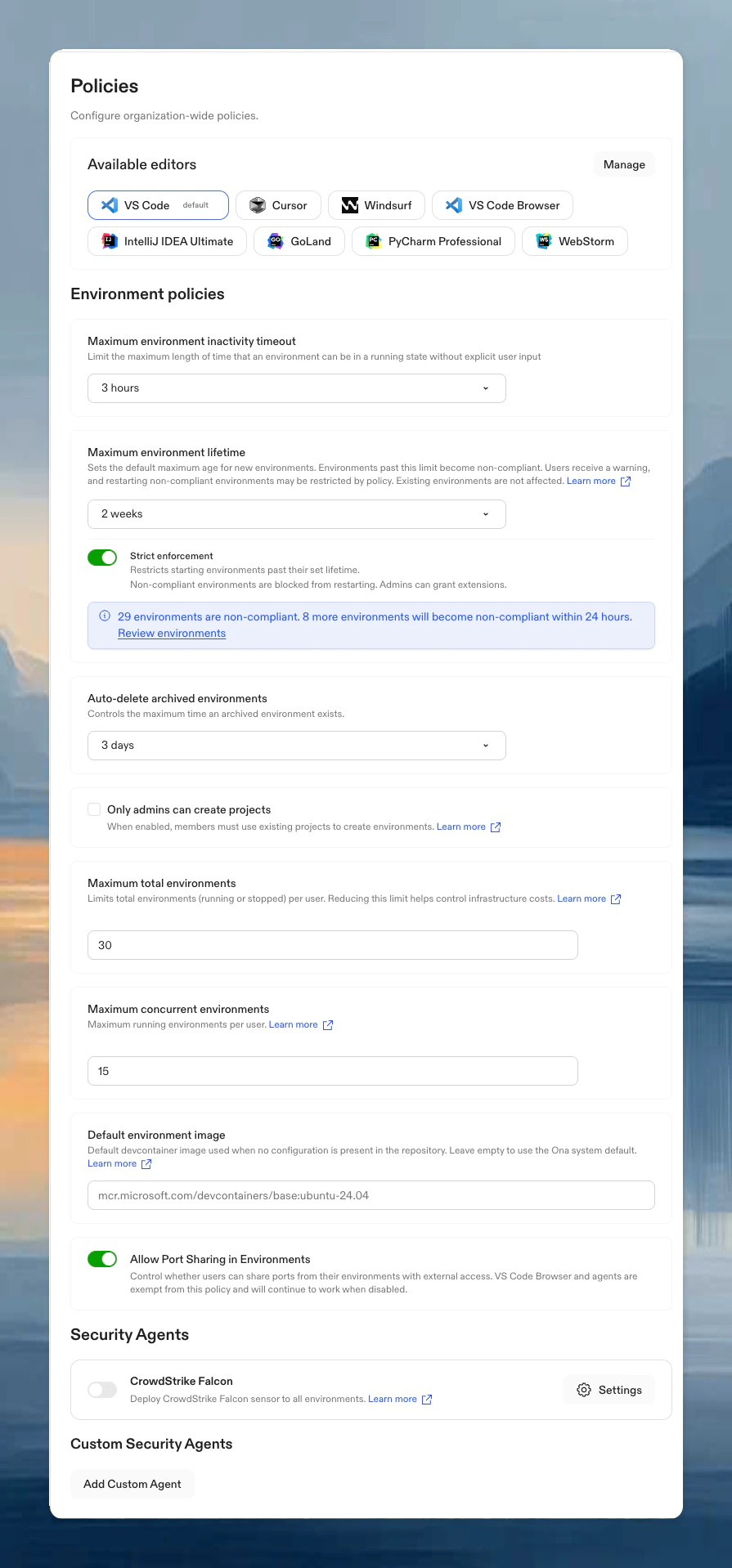
Available policies
| Policy | Purpose |
|---|---|
| Editor restrictions | Standardize which editors and versions your team can use |
| Environment timeout | Limit auto-stop timeout options |
| Environment limits | Cap total and concurrent environments per user |
| Maximum environment lifetime | Set a maximum age for environments and optionally block restarting expired ones |
| Archive timing | Set when stopped Enterprise environments move to Archived |
| Environment creation | Restrict blank environment creation for members |
| Project creation | Restrict project creation to admins; members must use existing projects |
| Port sharing | Control user-initiated port exposure from environments |
| Default image | Set default devcontainer image |
| Auto-delete | Set retention period for archived environments |
| Security agents | Deploy CrowdStrike Falcon to all environments |
| Executable deny list | Block specific executables from running in environments |
| Command deny list | Block specific commands from Ona Agent execution |
| SCM tools | Control Ona Agent’s GitHub/GitLab access |
| Restrict account creation to SCIM | Allow only SCIM-provisioned users to access the organization |
Looking for default environment image settings? See Default image policy.
Tracking changes
All policy changes are recorded in audit logs, including who changed what and when.Best practices
- Start gradually: Begin with moderate limits and adjust based on usage patterns
- Review regularly: Check usage patterns quarterly or after team changes
- Avoid over-restricting: Use environment creation restrictions before requiring project-based creation for all member environments