Project secrets are scoped to a single project. Anyone who launches an environment from the project gets these secrets injected automatically. Use them for credentials the whole team needs for that repository (API keys, service accounts, registry access) without exposing them to other projects in the organization. Project secrets have middle precedence. They override organization secrets but can be overridden by user secrets. Teams set project defaults while individuals can still customize.Documentation Index
Fetch the complete documentation index at: https://ona.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
Common uses
Project secrets are the right default for credentials tied to one repository or workflow. Typical examples:- API keys for services used by one codebase
- shared test credentials
- project-specific registry access
- configuration values that should travel with the project rather than the whole organization
Manage project secrets
Navigate to Project → Secrets.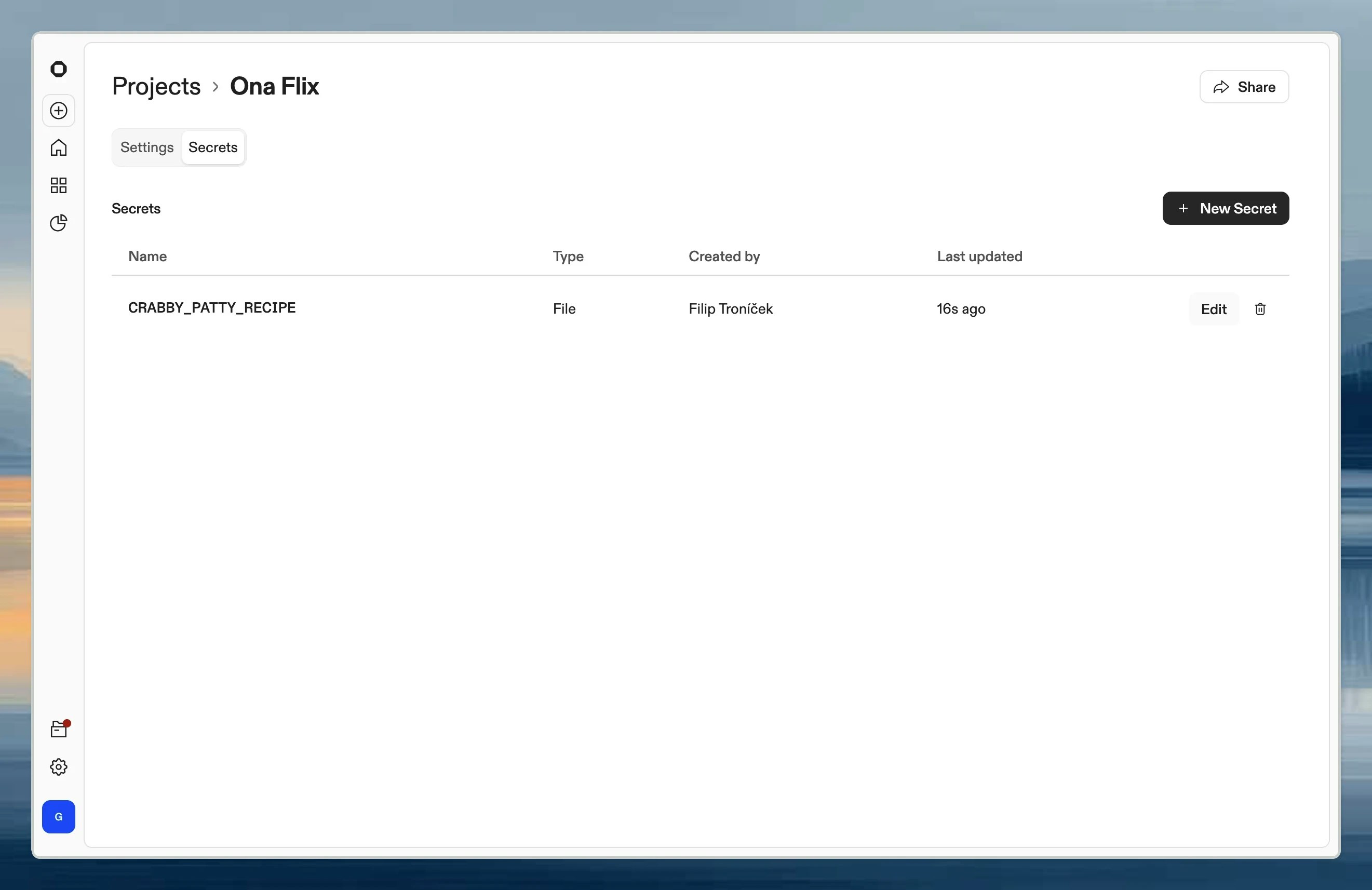
When to use project secrets
- Shared service accounts: Database credentials, API keys for project-specific services
- Project configuration: Environment-specific settings the whole team needs
- Container registry access: Private images for this project’s Dev Container