Ona integrations fall into three categories:Documentation Index
Fetch the complete documentation index at: https://ona.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
- Source control for cloning repositories, pushing commits, and letting agents interact with pull requests and issues
- Tool integrations for giving agents access to work trackers, docs, incident tools, and other MCP-backed services
- Cloud access for federating from environments into providers like AWS without long-lived credentials
Source control
Source control is the foundational integration in Ona. It gives environments access to your repositories and lets agents work with the same permissions your developers already have. Supported providers:| Provider | Repo access | Agent API tools |
|---|---|---|
| GitHub | Yes | Yes |
| GitLab | Yes | Yes |
| Bitbucket Cloud | Yes | No |
| Azure DevOps | Yes | No |
Tool integrations for agents
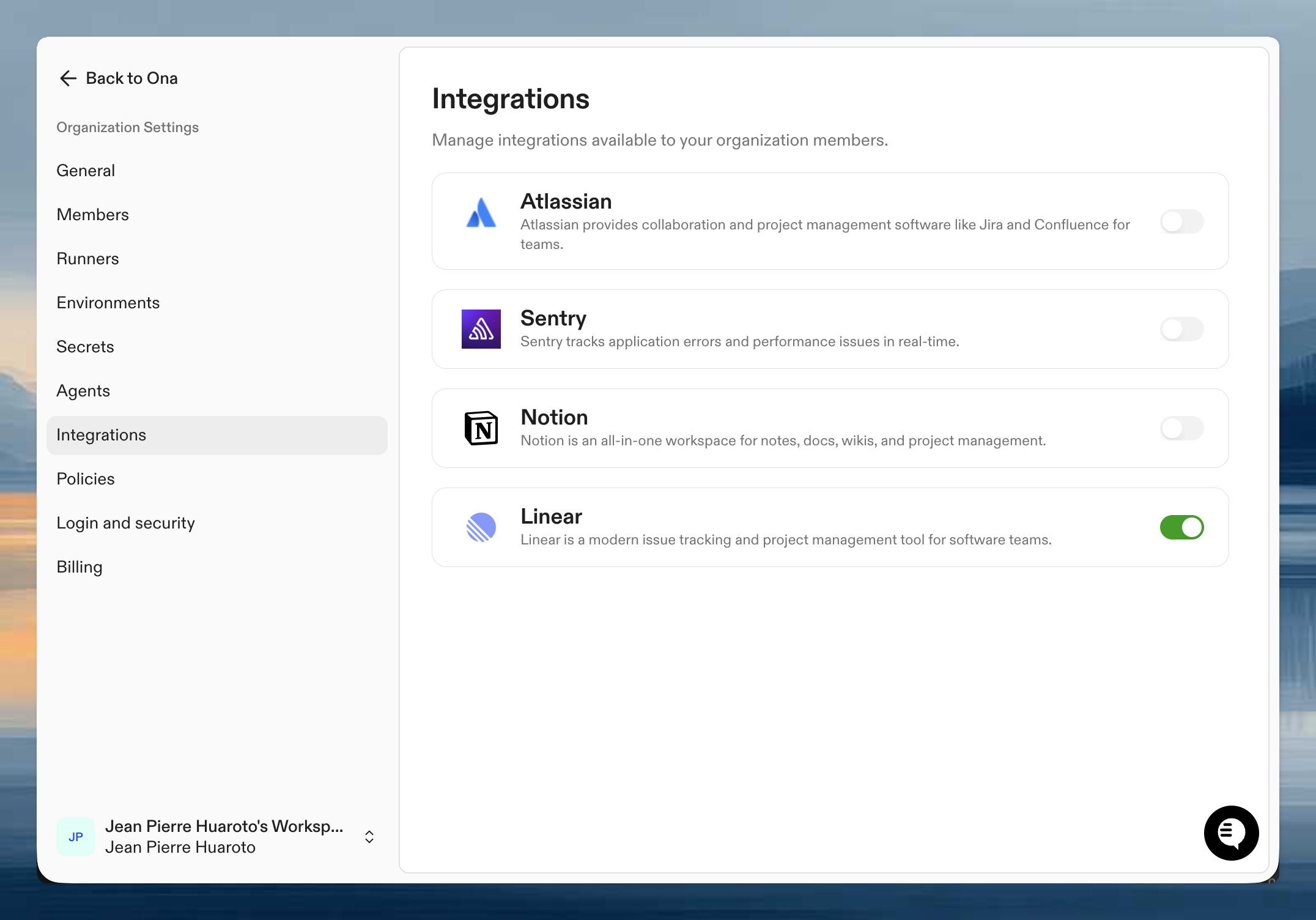
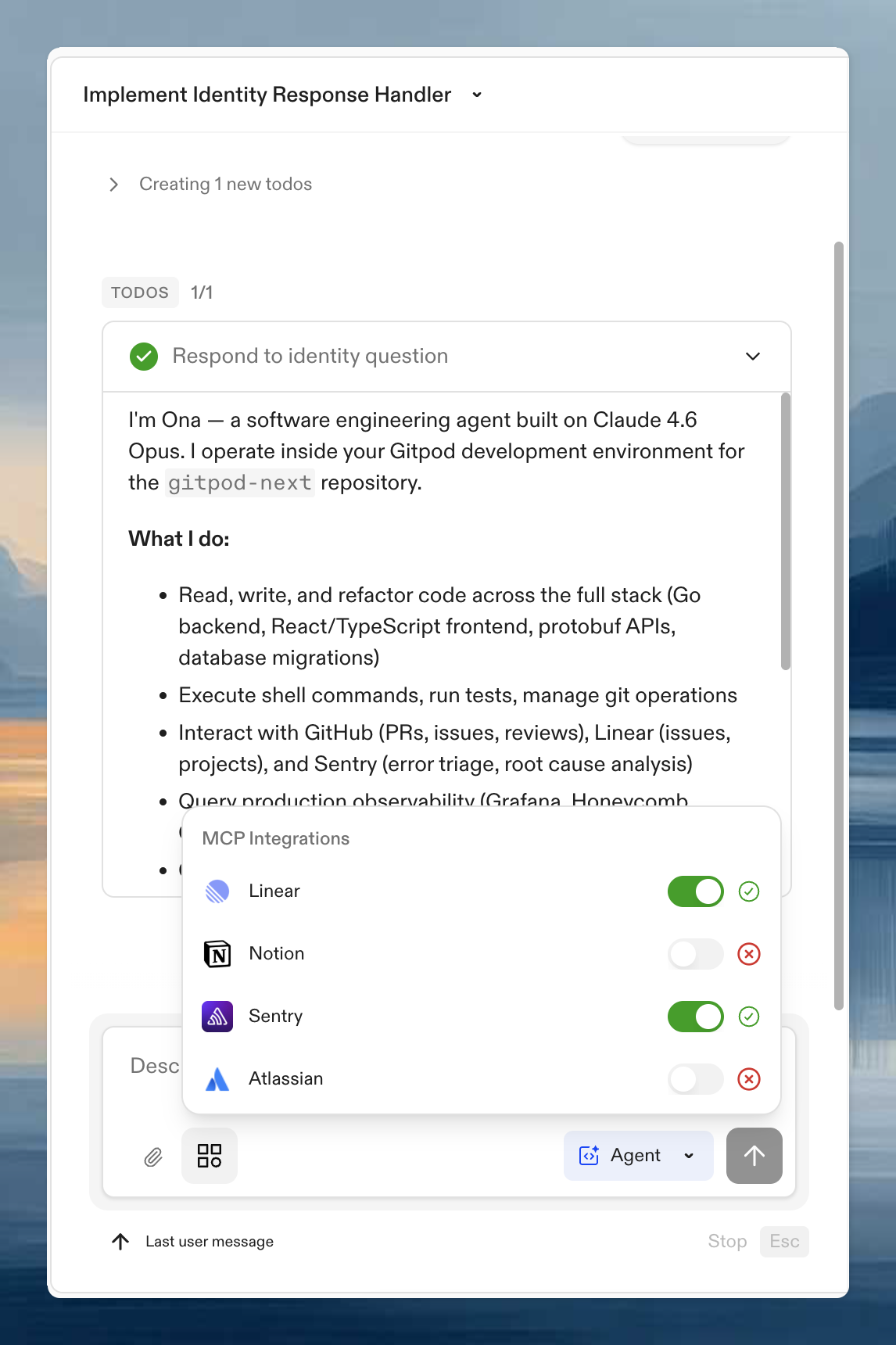
Most non-SCM integrations are exposed to agents through the Model Context Protocol (MCP). There are two distinct layers, and both must be in place before an agent can use a tool:- Organization integrations are configured by an administrator in your organization settings. They turn an integration on for the org (e.g., “Linear is allowed in this organization”) and provide the OAuth client and any shared configuration. Without this, the integration does not appear to users.
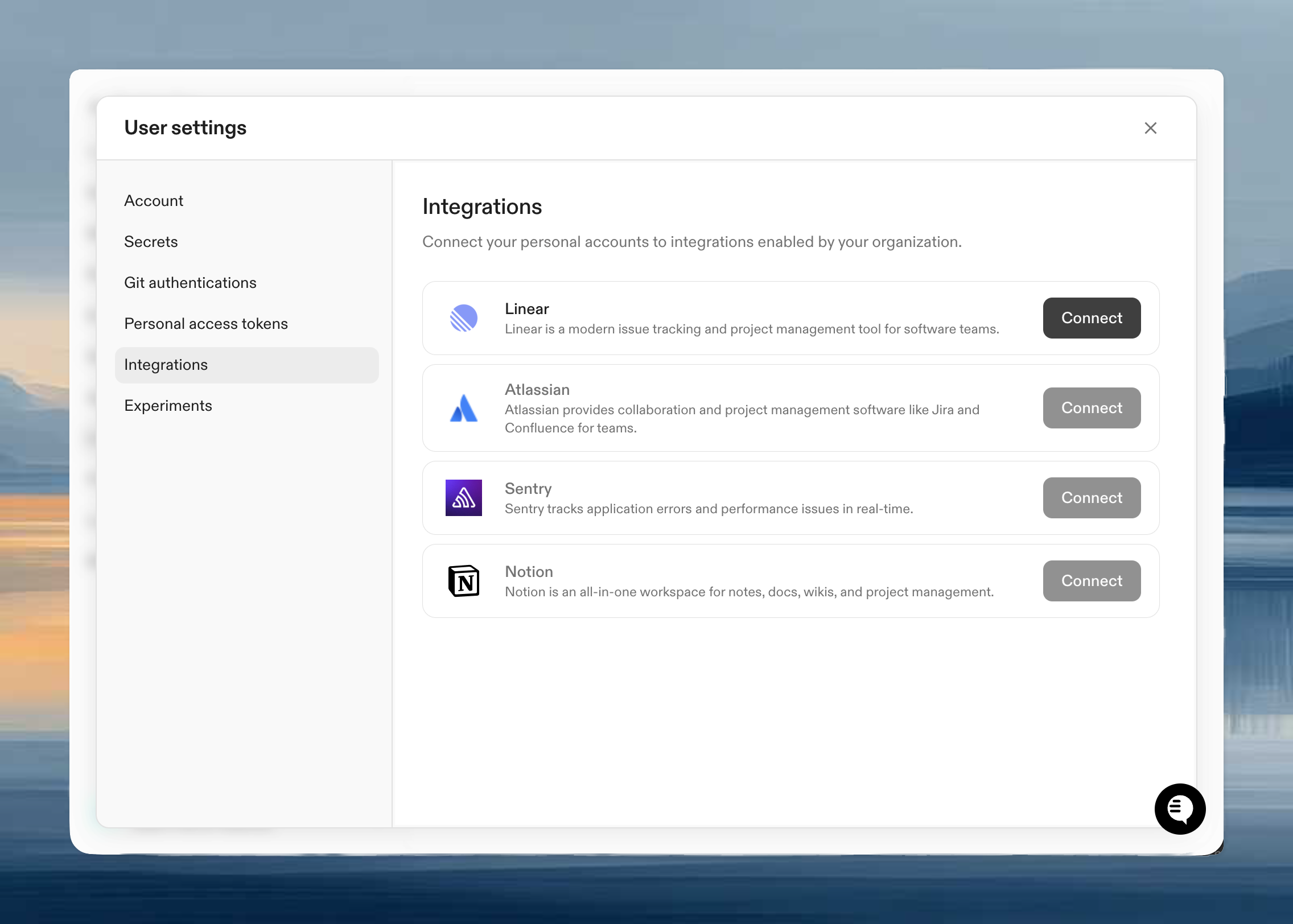
- Per-user MCP authentication happens after the org integration is enabled. Each user authenticates the integration with their own account so the agent acts with their permissions, not a shared service account.
- Organization-level enablement by an administrator
- User authentication so the agent acts with your permissions
| Integration | What agents can do | Setup |
|---|---|---|
| Linear | Read issues, update status, use backlog context | Configure Linear |
| Atlassian | Work with Jira and Confluence | Configure Atlassian |
| Notion | Search and read workspace docs | Configure Notion |
| Sentry | Inspect errors and issue context | Configure Sentry |
| Granola | Search meeting notes and transcripts | Configure Granola |
| GitHub App | Mention @ona-agent on a pull request to start an agent on the PR | GitHub App |
Cloud access
Ona environments can also federate into cloud providers using short-lived credentials instead of static secrets.- OpenID Connect (OIDC) for the core model
- AWS access from Ona for the AWS-specific setup